The stablecoin staking aggregator, Zunami, has fallen victim to a price manipulation attack that resulted in a staggering loss of approximately $2.1 million from the protocol.
Security Breach Rocks Zunami
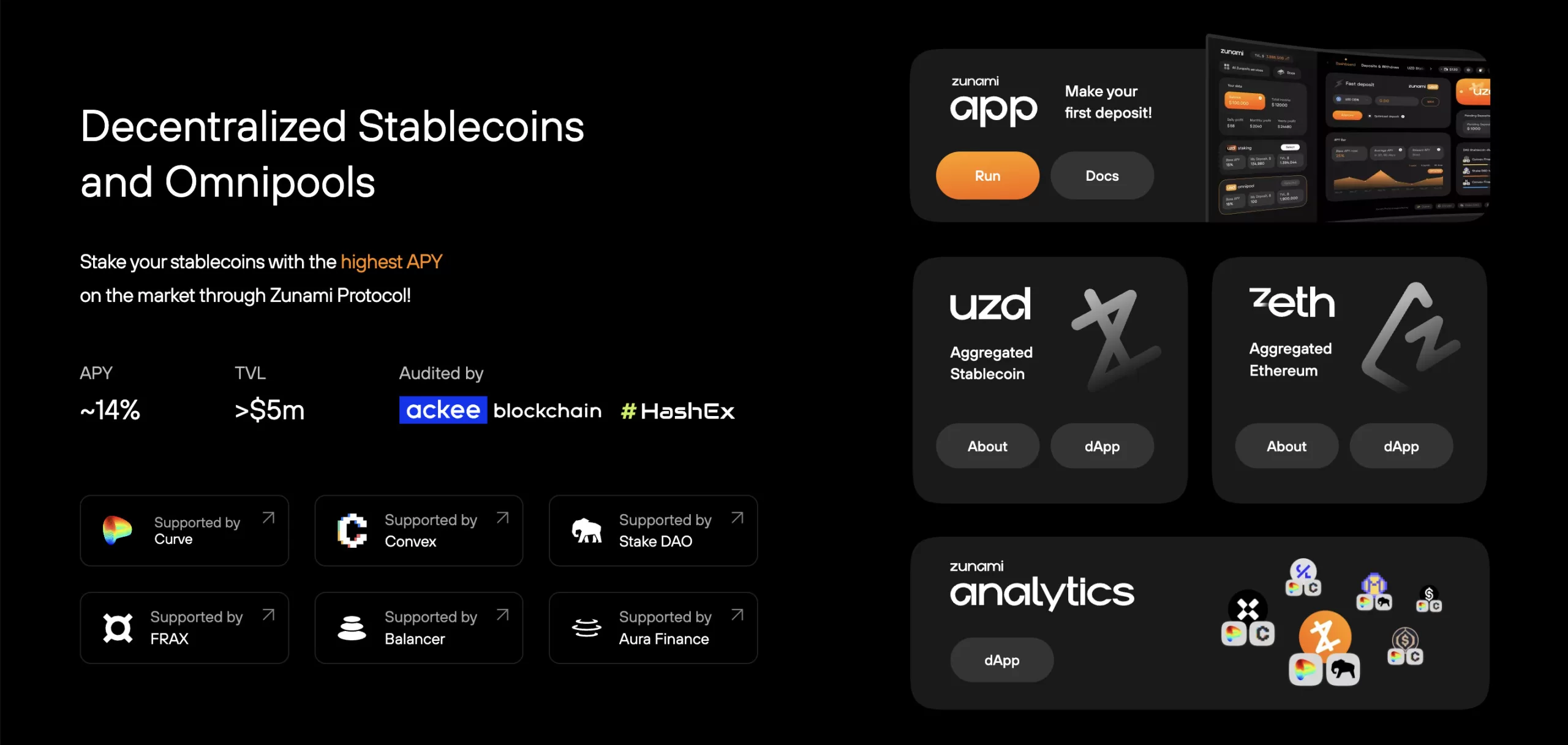
Zunami, a platform that specializes in stablecoin staking, recently faced a severe blow as it became the target of a price manipulation attack. In a startling incident, a hacker executed a meticulously orchestrated exploit that allowed them to make away with a substantial sum of around $2.1 million from the protocol’s funds.
Security Firm Unveils the Attack
PeckShield, a blockchain security company, was the first to identify the vulnerability in Zunami’s security. The firm took to its official channels to announce the ongoing attack, urging users to take immediate and necessary actions to safeguard their assets. A subsequent post by PeckShield confirmed the grim outcome, indicating that the hack led to a staggering loss exceeding $2.1 million.
Targeting the Heart of the Protocol
The attack zeroed in on Zunami’s zStables pool, a vital component of the protocol’s operations. A post from Zunami confirmed the severity of the incident, warning users against purchasing zETH and UZD due to the compromised emission of these stablecoins resulting from the attack.
Drastic Losses Ripple Through
In the aftermath of the exploit, Zunami’s stablecoin UZD experienced a drastic plummet of 99%, plummeting its value to an alarming $0.001. Similar to this, CoinGecko reported that its zETH stablecoin’s peg to Ether had broken, resulting in an 87% decline in value from its pre-exploit valuation.

The Cryptic Trail to Concealment
The attacker’s maneuver to conceal the stolen funds adds an intriguing layer to the incident. By sending the ill-gotten gains to Tornado Cash, a crypto mixer protocol, the assets become significantly harder to trace back to their original source. This choice to utilize an obfuscation technique raises questions about the attacker’s motives and strategy.
As the cryptocurrency landscape continues to navigate the complex world of security vulnerabilities and exploits, Zunami’s incident serves as a reminder of the critical need for heightened security measures. The aftermath of this attack leaves both the protocol and its users facing significant losses, emphasizing the paramount importance of staying vigilant and informed in the ever-evolving realm of digital assets.







