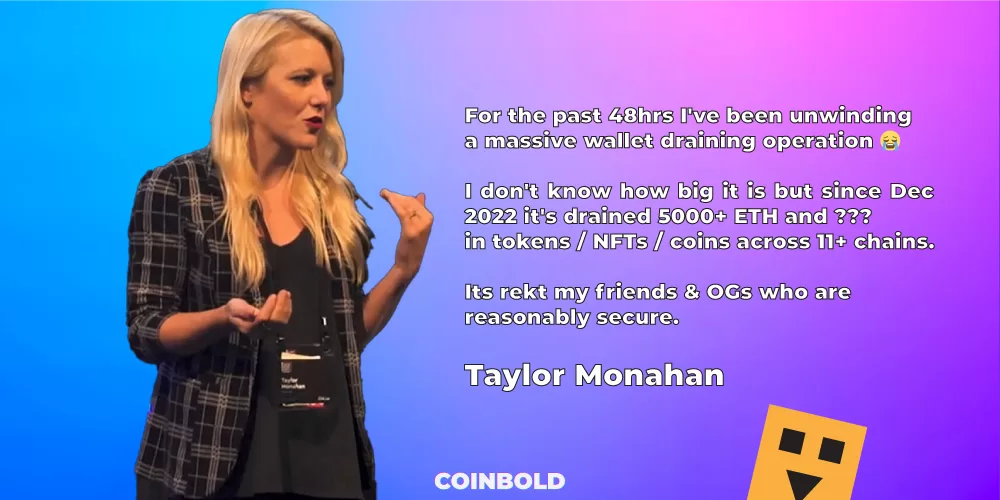
Taylor Monahan, founder of Ethereum wallet manager MyCrypto, revealed a sneaky cyber attack that reportedly siphoned off more than $10 million from early adopters of cryptocurrencies since December, shaking the entire crypto space.
She said that approximately 5000 ETH tokens, with a market value of $10.4 million at the moment, had been stolen.
The fact that this attack even targeted hardware wallets—the purportedly most secure wallets for storing cryptocurrency—makes it all the more devastating.
Unexpectedly, the origins of an attack that only targets pro-crypto users “who are reasonably secure” remain a mystery.
This is NOT a shady con artist or a lowbrow phishing site. NOT ONE NOOB HAS BEEN REKT BY IT. ONLY OGs are rekt by it.
But common themes emerged among all impacted users. All affected wallets’ private keys were generated between 2014 and 2022, giving them a long history in the cryptosphere, including numerous addresses and other things.
She only provided two pieces of advice in a tweet: don’t keep secret phrases for longer than a year or hold all of your cryptocurrency assets in a single key. To lessen the impact of such cyberattacks, it is advisable to divide cryptocurrency assets among different wallets.
Taylor Monahan claims that someone may have amassed a significant amount of data over the years, which he is methodically utilizing to exploit private keys in order to steal money.
According to the most recent information about the attack, the cyberattack appears to have been skillfully executed and is quite unique.
1. Primary theft transactions (first direct attack on the wallet) are mostly happening between 10 am–4 pm UTC.
2. Secondary theft transactions (transactions after attacks) are commonly executed between 4 pm-10 pm UTC.
3. The attacker swaps users’ tokens inside the users’ wallets before stealing. For that instance, it uses MetaMask Swaps, Uniswap, or 0x.
4. Users’ staked tokens, NFTs, and less popular tokens stay untouched.
5. The attacker transacts a small number of tokens between different affected wallets and when there are enough amount in one address, it finally moves out.
6. The “out” transactions were made through centralized swappers, like FixedFloat, SimpleSwap, SideShift, and many more.
7. All stolen funds were ultimately converted into Bitcoins, which transaction mostly happens in the day.
8. Surprisingly, the attacker has utilized the MetaMask wallets to transact. However, Taylor Monahan made clear that not only MetaMask but all types of wallets are compromised in the attack, so, it is not only a MetaMask attack.
9. After the first attack, the attacker came back 80 days after to steal the remaining amounts of tokens.